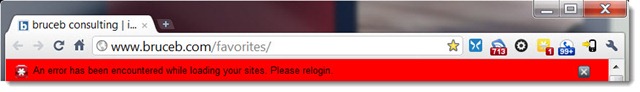
If you are a LastPass user, you may be required to change your master password. You will be prompted by the program if that’s necessary – for example, you may see the red browser toolbar pictured below. When you log in again, you’ll be led through a short process to pick a new master password.
[Update 05/06 1:30pm: The company has stopped requesting master password changes until its database catches up after two very busy days. If you see the request in the future, you will have the option not to change your master password if you know that it is strong. There’s up to date info in the company blog.]
On Wednesday afternoon, LastPass announced that it might have been hacked and was immediately taking this step as a precaution against the possibility that anyone’s passwords might be exposed. That sounds awful but your risk is nearly zero. The company will likely come out stronger because it announced the situation promptly and dealt with it in a responsible way.
Let me say this as plainly as I can.
There are many things to worry about in this world. This is not one of them.
Trust LastPass. Use it with confidence.
After putting together information from the various blogs and interviews and articles (here and here and here, for example), this seems to be where things stand.
- On Wednesday, the company noticed unusual network activity almost immediately after it occurred. It concluded that it could not account for a small amount of data that had left the network. Based on the amount of data traffic, it’s possible that data was removed by hackers for a handful of LastPass users – a couple of hundred at most.
- The data is heavily encrypted. There is one, and only one, way that it could be decrypted: if the user has picked a master password that is a simple dictionary word, and the hackers successfully run a dictionary attack on the data. Based on that remote possibility, the company decided to react strongly by requiring master password changes and verification of user identities.
- If you have a strong master password, you are not at risk. If your master password has an upper case letter or two, a number, or a symbol, your password is essentially unbreakable. From an interview with the CEO:
- “PCW: If someone had what you’d consider a strong master password, then, would they have any reason to be worried at this point?
- “Siegrist: No. None.”
- The chances are high that no one is at risk and the company is overreacting. There is no evidence of any significant breach. In some sense any breach is significant, but this has zero relationship to the monumental, horrible security disasters that have been in the news lately – the massive Sony Playstation Network breach, plus Epsilon, RSA, and others. Those are breaches to worry about. This one is not.
As I understand it, LastPass does not have your master password and literally cannot decrypt your passwords at all. I’m seeing that reported inaccurately and it’s important to know. LastPass does not have a “master password database.” It doesn’t have a record of your master password anywhere on its servers. When you supply your master password, you are supplying a cryptographic key that is used by your computer to decrypt the database held by LastPass. Note carefully how that works! The decryption is done by your computer, not by the LastPass servers; LastPass cannot decrypt your passwords at all. If a hacker broke into the company headquarters and walked out with the LastPass servers, your passwords would still be safe.
Your life will continue to be filled with passwords. The way to be safe has not changed: use different passwords on each web site instead of repeating the same one over and over, and use LastPass to store them so they’re not written down or stored on a memory stick that’s easy to lose. And be careful out there!