
Ed Bott has written a fascinating article about Java’s bad behavior – not just its security vulnerabilities, which are legion, but also its incessant attempts to install adware that mucks up your computer every time you install an update. It’s a must-read article if you want to know how your browser winds up infested with cruddy toolbars and hijacked home pages and the wrong search engine.
After the hubbub ten days ago about a dangerous flaw in Java, you should already have a poor opinion of it. It’s even worse than you think. There are still good reasons to uninstall Java or disable it in your browsers, even after the latest patch, and Oracle’s packaging of adware with each update is just obnoxious. You might have to use Java for some program or web site that requires it but treat it with distaste and extra caution.
SECURITY
Java’s security continues to be questionable. Within 24 hours after Oracle delivered the critical Java 7 Update 11 patch on January 13, bad guys were reportedly circulating another unpatched zero-day vulnerability. Separately, researchers reported yesterday that they had found two more previously unknown flaws that were not fixed by the Java 7 Update 11 patch. Those are not in the wild – yet – but it increases the pressure on Oracle to deliver yet another patch lickety-split.
Oracle is going through the hardening process that Adobe endured a couple of years ago. It’s an ugly process. If Oracle gets its act together, Java will eventually be automatically updated on a predictable schedule and attention will drift away. We’re not there yet. At the moment Oracle is a leading member of the security Hall Of Shame.
ADWARE
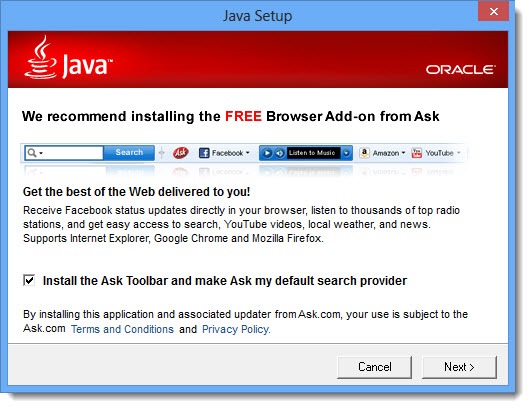
When you use Java’s update program, it always includes third-party adware crap. Not just the first time, like many other programs (Adobe and Skype, we’re looking at you), but every time an update is released. That’s eleven updates to Java 7 in the last 18 months, eleven times you might have accidentally picked up a junk toolbar or had your browser search provider hijacked.
This is the step that installs the crappy Ask Toolbar and changes your search provider – with the checkbox checked by default:
Ed Bott discovered a deceptive trick built into the Ask Toolbar installer. Imagine that you realize too late that you missed the checkbox. You open Control Panel and look at the list of installed programs and sigh in relief because there’s no new entry for the Ask Toolbar. Dodged the bullet, right?
The installer for the Ask Toolbar has a timer that delays the installation by ten minutes. After ten minutes it drops the toolbar on your system and alters your browser settings.
There is no legitimate reason for that delay. It’s one more way to fool you into getting this junk on your computer. It’s part of a pattern of behavior designed to prey on users.
The Ask Toolbar is actually a lightly customized version of a toolbar distributed by IAC, an Internet media conglomerate controlled by Barry Diller. IAC distributes junk toolbars with a dizzying variety of branding. Security researcher Ben Edelman has written a lengthy analysis of the IAC/Ask toolbars. Relevant excerpts:
“IAC’s search advertising business exists not to solve a genuine user need or provide users with genuine assistance, but to prey on users who — through inattention, inexperience, youth, or naivete — stumble into IAC’s properties. . . .
“A security update should never serve as an opportunity to push additional software. As Oracle knows all too well from its recent security problems, users urgently need software updates to fix serious vulnerabilities. By bundling advertising software with security updates, Oracle teaches users to distrust security updates, deterring users from installing updates from both Oracle and others. Meanwhile, by making the update process slower and more intrusive, Oracle reduces the likelihood that users will successfully patch their computers. . . .”
Your Internet browser now blocks add-ons like the Ask Toolbar until you approve them. The Ask Toolbar installer adds big arrows and official-looking instructions to fool you into approving the add-on. The instructions and arrow above the red line are from Ask, not Microsoft, in this example from Internet Explorer:
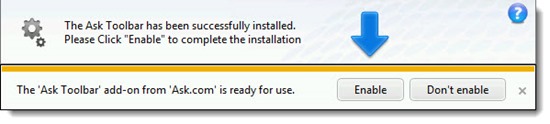
Sleazy stuff.
SEARCH PROVIDER
This also ties into my last article about doing web searches from the address bar in your browser, using a default search provider – usually Google.
The Ask Toolbar installer changes your default search provider, so your web searches produce crappy, ad-laden results – filled with advertisements that are laid out deceptively to make paid ads indistinguishable from useful results, and all too often including deceptive or misleading links.
Ed Bott and Ben Edelman both demonstrate ways that Ask search results flout industry practice and Google rules. Edelman: “In short, a user viewing IAC results gets listings that are intentionally less useful — designed to serve IAC’s business interest in encouraging the user to click extra advertisements, with much less focus on providing the information that IAC and Google consider most useful.”
Apparently Ask changes the default search provider in all browsers – IE, Chrome, and Firefox – and does not reliably set things back when the Ask Toolbar is uninstalled.
Your searches in your browser should be handled by Google, or whatever you choose for yourself. If your searches are hijacked, follow the instructions in the article to set them back to your choice.
Think about uninstalling Java. If you have a program that requires Java, consider doing without that program. Oracle deserves to lose your trust and respect for a while.

Trackbacks/Pingbacks